If there is a protection manager, its checkConnect system is known as While using the neighborhood host name and -1 as its arguments to view If your Procedure is authorized. If your operation is not really authorized, an InetAddress symbolizing the loopback address is returned.
The element might be both a DOM factor or simply a CSS selector. After the functionality is known as, the element inline types is going to be up-to-date to render the avatar.
Desktop wallets are program apps you download and set up on your personal computer. Desktop wallets present Increased attributes owing to PCs�?better processing power, which include Innovative portfolio management tools.
You signed in with A further tab or window. Reload to refresh your session. You signed out in A further tab or window. Reload to refresh your session. You switched accounts on another tab or window. Reload to refresh your session.
Now develop a JSON file named composer.json in your task directory and copy-paste the following in it.
is a activity-theory principle that assumes various entities will usually default to a typical Option to a difficulty in absence of any communication. Schelling-point mechanisms are frequently Utilized in decentralized oracle networks to allow nodes get to consensus on solutions to information requests.
A Liquidity Pool Visit Site pair (e.g. an UniswapV2 Pair) will mechanically be created on copyright or PancakeSwap in the course of token deployment. Token operator can established an initial source amount to add towards the liquidity pool and may opt to lock LP tokens eternally in the token contract or acquire them inside their wallet.
This oracle node can query info resources—using application programming interfaces (APIs), by way of example—and ship transactions to keep the requested knowledge while in the good deal's storage.
Various oracles give different answers on the oracle difficulty, which we check out later on. Oracles are generally evaluated on how perfectly they can deal with the following issues:
For every transaction a price will automatically be divided among the token holders to reward them. Operator can exclude some accounts within the cost or from your reflection mechanism.
According to situation seventy six (#seventy six) I have made a decision to also archive this repository to further decrease possibility that somebody uses this Instrument. The code won't recieve any updates and i have still left it within an uncompilable point out. Use another thing!
Although this can be a swift method, There exists a possibility that miners will retain the private vital that generated the address and use it Later on to hack your resources and steal the tens of millions stored in your vanity address.
Subscribe to our publication for more content and guides on Ethereum. In case you have any feed-back, experience free to achieve out to us by using Twitter. You could normally chat with us on our Discord Local community server, that includes a lot of the coolest developers you’ll at any time fulfill :)
How can we verify which the injected details was extracted from the proper supply or hasn’t been tampered with?
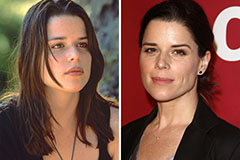 Neve Campbell Then & Now!
Neve Campbell Then & Now! Alana "Honey Boo Boo" Thompson Then & Now!
Alana "Honey Boo Boo" Thompson Then & Now! Tiffany Trump Then & Now!
Tiffany Trump Then & Now! Erik von Detten Then & Now!
Erik von Detten Then & Now! Lisa Whelchel Then & Now!
Lisa Whelchel Then & Now!